It took me longer than I expected to finish the first part of “A Storm of Swords“, but it was definitely worth the effort. And I say effort because after thousands of pages that I mostly read through the night, the multitude of names starts makes it hard to follow the chain of events and alliances without taking notes and running back to consult them. And that is why I am thankful for the Wiki of Ice and Fire.
Category: Uncategorized
3rd Infocom Security (Athens)

Yesterday I managed to attend the 3rd Infocom Security event here in Athens. It was a full house, given the fact that the registration queue was so long that I gave up and went for coffee for half an hour before returning to the desk. Such a high attendance was to be expected, since this is a “free of charge” event. I saw almost all familiar faces (whether we’ve been introduced or not) that I see in other events and gatherings which are considerably smaller. This only makes it a success.
For as long as I stayed there, I was on the hallway track. It was too difficult to secure a place within the halls, so I wandered around the booths with a lot of other attendees. The most interesting one IMHO, was by census since these guys did something that the others did not: The displayed a zero day exploit. Quite impressive stuff accompanied by an excellent and thorough technical explanation. In the end I had an interesting exchange with them that went along these lines:
– Since you are not in the exploit selling business, why are you showing this to me here?
– We aim to show that even when you do your best (and most do not) you may end up with a false sense of security. And we aim to help you with that.
A lot of people opt for the blue pill and take a bet: things won’t break while they are in office. Even competent people put their heads in the sand sometimes.
So there, it was a “red pill” presentation, quite different from the typical “blue pill” ones that we’re used to. And the best thing that I got from the event.
—
#include<std/disclaimer.h> /* I have known the census people for some years and share a graduate supervisor with one of them */
milter-greylist
After years of using graymilter (with a series of local hacks) I switched to milter-greylist.
After it run for a few days:
# Summary: 149173 records, 137182 greylisted, 11991 whitelisted, 0 tarpitted
and with only a few tweaks in its configuration:
racl whitelist domain google.com racl whitelist domain googlemail.com racl whitelist domain gmail.com racl whitelist domain yahoo.com racl whitelist domain hotmail.com racl whitelist domain live.com racl whitelist domain outlook.com racl whitelist domain amazon.com racl whitelist domain ebay.com #racl whitelist domain gr racl greylist default
You can apt-get install milter-greylist (which makes maintenance through OS upgrades manageble) and it has all the features that I would love to add in my series of hacks to graymilter but never got around to doing so.
(previous)
networks of networks
In John Gall’s “Systemantics” two laws that play important role are stated:
- Systems tend to expand to fill the known universe, and
- Every system is part of a larger system*
So when I read this tweet by Steven Strogatz:
Interdependent networks, aka “networks of networks” = the next big thing in network theory? http://www.wired.com/wiredscience/2013/03/math-prevent-network-failure/all/ …
I was tempted to rephrase them as:
- Networks expand to fill the known universe
- Every network is part of a larger network (remember there is no air gap, only different kinds of latency)
Gall’s laws never stop to amaze me.
[*] – This statement actually belongs to Grady Booch who uses it while discussing Gall’s Laws of Systemantics in his “On Architecture” podcasts.
Όχι άλλο χώσιμο
Ταβάνι number 2
“ο νέος ρόλος τον οποίο καλείται σήμερα να διαδραματίσει ο CIO, είναι ιδιαίτερα αναβαθμισμένος σε σχέση με το παρελθόν «αφού συμβάλλει ως μέλος πλέον της ηγετικής ομάδας, στη χάραξη της στρατηγικής της εταιρείας».”
Χαντρούλες στους ιθαγενείς, μια και όταν τα πράγματα είναι δύσκολα ο CIO κάνει operate (είτε inhouse, είτε outsourced) ένα cost center.
“ο CIO οφείλει σήμερα να συμβάλλει αποτελεσματικά στην ευθυγράμμιση του ΙΤ με το business με το να καταθέτει συχνότερα τις καινοτόμες προτάσεις του, μέσα από τις οποίες η εταιρεία του αποκτά το στρατηγικό πλεονέκτημα που της είναι απαραίτητο, προκειμένου να διαφοροποιηθεί σημαντικά από τον ανταγωνισμό.”
Εάν αυτό ίσχυε και οι προτάσεις του γίνονταν δεκτές, θα είχε σπάσει το ταβάνι, σωστά;
Do not tell me; show me.
Dancing with Elves
“Human interaction is a game, a dance, a playful thing that is deeply satisfying in itself” – John Gall
I got to read John Gall’s “Dancing with Elves” after reading his well known “Systems Bible” (for which I’ll blog another time). The book deals with strategies that one can use in order to influense kids in a positive way so as to achieve what the parent wants the kid to achieve. By that we do not mean to pre-plan the child’s life and then watch as the plan gets executed. This is not the plan. The plan is to overcome furstration (and disobedience) and find out strategies which will help the child arm itself before being released into the world as a responsible adult that does not require parental supervision.
I have to admit that the fifteen strategies presented in the book are interesting. They all strive to make the parent not say “no” or use any other negative, derrogatory or yelling arguments to have a point pass. Like the author says “don’t oppose forces- utilize them”. The strategies may seem conflicting, but Gall as an accomplished paediatrician undrestands that there is no unique strategy that would fit all children, or even one child all the time. So one of the first things that parents need to realise, is that you have to use the strategy that works at the given time and situation. And be prepared that it may not work some time afterwards. I think the message of the book is: Everytime you want to yell to make a point, can you do it without yelling? Here’s how.

A book about (systems) management
I do not know how well am I going to use advice from the book as a parent, but this book is more than a parenting book. It is a management one. At least within the IT business where childish, erratic or other BOFH style behavior is common. This occured to me when reading that
“although every picture tells a story, the story it tells may not be the same for everyone. The meanining of communication is what the other person makes of it, and that’s not necessarily the same as what you intended. It’s up to you to notice that. That’s your feedback.”
Compare the above to the everything is a DNS problem mantra. But then again there is also other management insight that most overlook:
“But what does it mean when you say a person is “just lazy” or “just stubborn”? It really means that you have tried out some of your repertoire of behavioral interventions in order to elicit desired piece of behavior from the other person and you have failed, because yoour repertoire was too limited.”
Yes dear manager of weird IT people, sometimes you have to admit that your repertoire is limited. You too have to change your approach to get the job done.
I loved the book. How could I not love a management book presenting itself as a parenting one which in the last pages includes the definition of the law of requisite variety?
[*] – image and phrase came from my twitter timeline, not from the book
OODA Loop and DevOps
I spotted on twitter the other day a Donkey Kong analogy for DevOps:
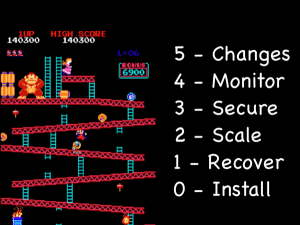
Regardless of how fun (and close to heart) it is, the analogy is flawed because it describes a sequence. We do not wait to compete all the steps in the ladder in order to get to the next level. Nor, do we restart only when a barrel hits us.
Fast transients is what we do. Fast transients is a term conceived by John Boyd and he first used it for air combat: “the ability to change altitude, airspeed and direction in any combination”. This is after all the essense of the Release Early; Release Often mantra. Push your system out in the wild so as to get a grasp of where the audience wants to direct it. Or plan for organized abandonment. According to Boyd, what matters most is the tempo of change: “fast transients suggeststhat -in order to win or gain superiority- we should operate at a faster tempo than our adversaries, or inside our adversaries’ time scales”1,2
So it is no wonder that I belive that although not so funny, the OODA loop describes how we work:

Because as Boyd wrote:
“Orientation isn’t just a state you are in; it’s a process. You’re always orienting […] A nice tight little world where there’s no change – dinosaurs; they’re going to die. The name of the game is not to become a dinosaur […] If you are in an equilibrium position, you’re dead”
Now think of that in terms of what you do just to keep current with the tools of the trade and what you do in order to monitor, manage and evolve your infrastructure.
[1] – A vision so noble, Daniel Ford
[2] – Which reminds me of the Nyquist sampling theorem
An online test for Benford’s Law
I’ve been fascinated with Benford’s Law ever since I read Mark Nigrini‘s “Digital analysis using Benford’s Law“. As part of the fun I’ve used it to check whether email subject length follows it. So I figured, why not make a check available online? And here it is:
– http://first-digit.appspot.com
You copy-paste your number series and the application displays a column chart of the occurences of the first digit and the theoretical occurencies expected.

Use it and tell me what you think. Many thanks to Vaggelis Tripolitakis for finding the first bug. Be gentle with it as it runs as a free Google App Engine service. Depending on my free time and feedback I get, I may add the rest of the tests that Nigrini describes (second digit, last digit and first two digit distributions).
If you like it very much, you can buy me the kindle edition of the second edition of Nigrini’s book.
![[awaiting translation]](https://managing.blue/wp-content/uploads/2013/03/2013-03-19.jpg?w=300&h=225)
![dolphin, by girl[0]](https://managing.blue/wp-content/uploads/2013/02/dolphin.jpg?w=300&h=225)